Check Point Research (CPR), a cybersecurity investigative team, discovered a gnarly Android malware called FluHorse. This sickening, malicious software has the ability to mimic legitimate apps, luring unsuspecting victims to its deceptive lair.
Making matters worse, FluHorse can lie dormant in your device for months, remaining undetected and flying under your radar. Check Point Research investigators called the threat “persistent, dangerous and hard-to-spot.”
What can FluHorse do?
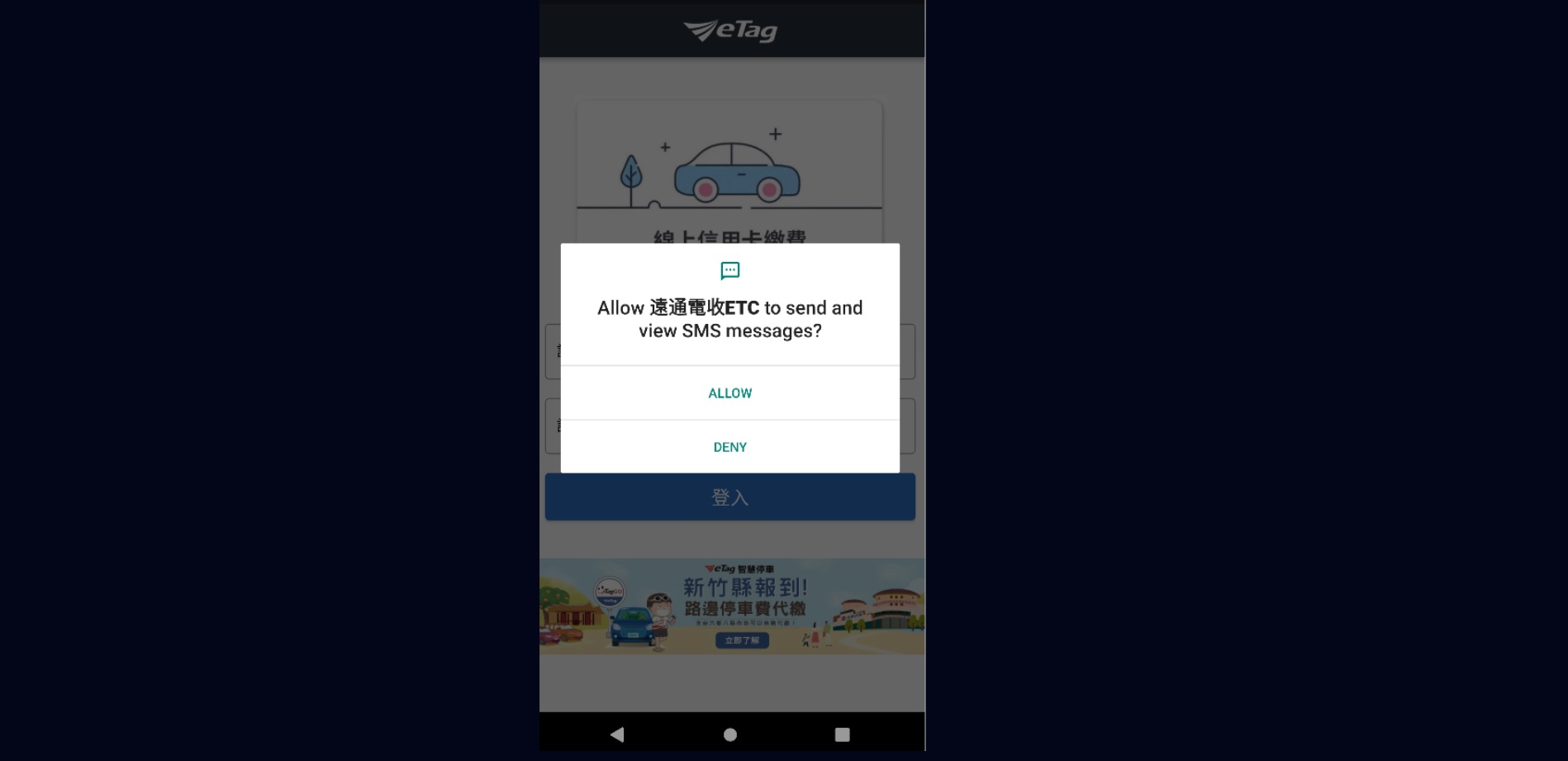
As mentioned, FluHorse’s modus operandi is mimicking genuine applications to mislead victims into its deceitful den. For example, investigators discovered that the malware masqueraded as a popular Taiwan-based toll collection app in Google Play.
According to CPR, the attackers behind FluHorse often imitated major banking and transportation apps, but the report did not disclose the names of these malicious apps. Most of these FluHorse-infected apps, according to CPR, have more than 1,000,000 installs. Yikes!
“The malware operators made an effort to carefully mimic all the key interface details to avoid raising any suspicions,” the CPR report said.
Once FluHorse wiggles its way into a victim’s device, it can steal their credentials and two-factor authentication (2FA) codes. How? Firstly, once the imposter app is installed, it asks victims to allow it to send and view SMS messages.
Next, quarries are prompted to input their credentials (e.g., password and credit card details). At some point, a command-and-control server intercepts any incoming SMS traffic to snatch 2FA codes. See how the malware works step-by-step with the diagram provided below.
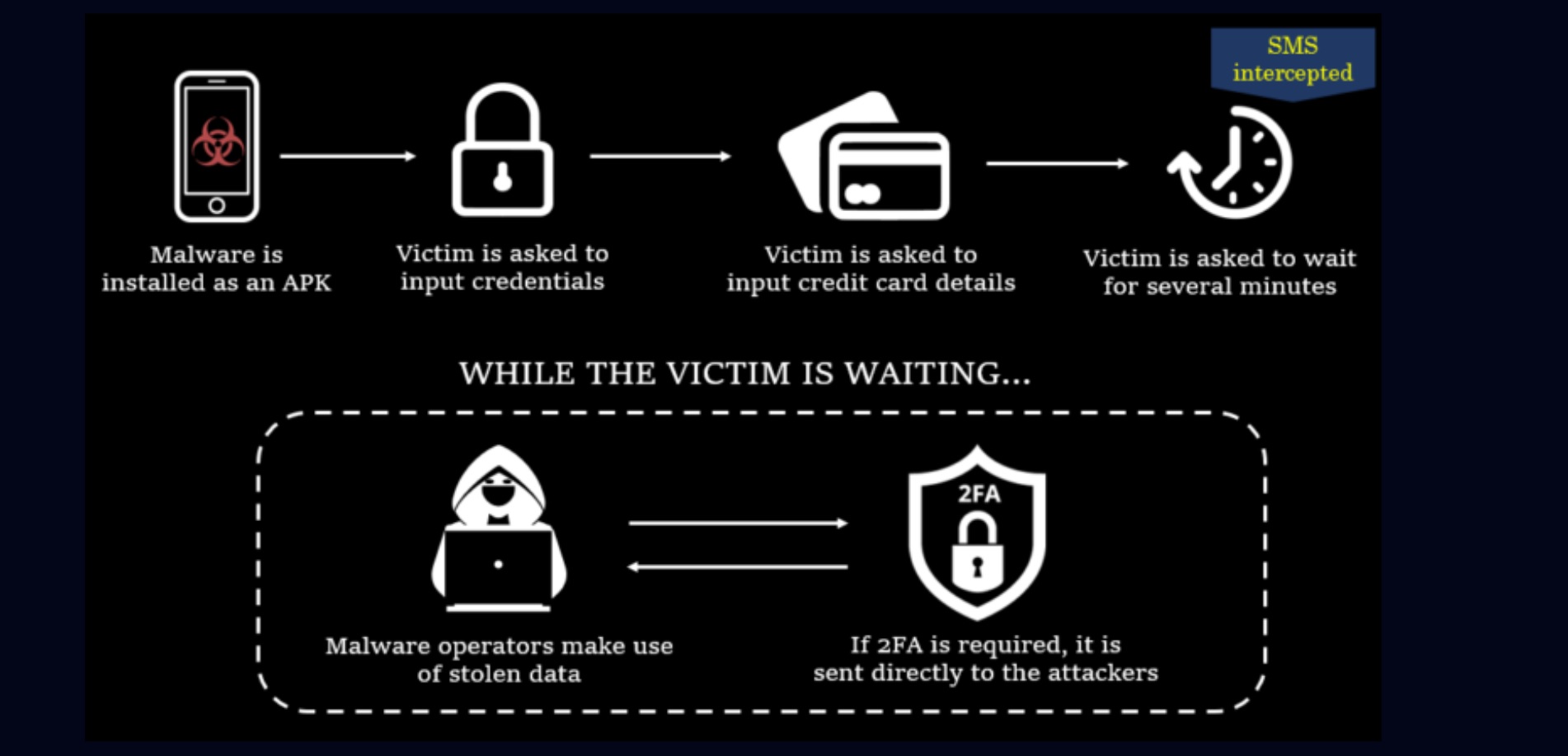
How do these FluHorse-infected apps end up on users phones? A sophisticated phishing campaign that lures victims to install apps as an APK. “We traced infection chains for different types of malicious applications and discovered multiple high-profile entities among the recipient of these emails,” the report said.
CPR noted that the framework that underpins these malicious apps is Flutter, a Google-created open-source software development kit. The Eastern Asian markets, according to CPR, were the main targets of FluHorse, but that doesn’t mean you’re off the hook if you’re outside of that region.
As always, the moral of the story is to avoid installing Android apps from non-reputable third-party app stores, suspicious emails, and other risky channels. The Google Play Store has its drawbacks, but it’s a far safer platform than the aforementioned sources.
Back to Ultrabook Laptops
Source link
 notebook.co.id informasi dan review notebook laptop tablet dan pc
notebook.co.id informasi dan review notebook laptop tablet dan pc